Court Filing Started a Furor in Right-Wing Outlets, but Their Narrative Is Off Track

WASHINGTON — When John H. Durham, the Trump-era special counsel investigating the inquiry into Russia’s 2016 election interference, filed a pretrial motion on Friday night, he slipped in a few extra sentences that set off a furor among right-wing outlets about purported spying on former President Donald J. Trump.
But the entire narrative appeared to be mostly wrong or old news — the latest example of the challenge created by a barrage of similar conspiracy theories from Mr. Trump and his allies.
Upon close inspection, these narratives are often based on a misleading presentation of the facts or outright misinformation. They also tend to involve dense and obscure issues, so dissecting them requires asking readers to expend significant mental energy and time — raising the question of whether news outlets should even cover such claims. Yet Trump allies portray the news media as engaged in a cover-up if they don’t.
The latest example began with the motion Mr. Durham filed in a case he has brought against Michael A. Sussmann, a cybersecurity lawyer with links to the Democratic Party. The prosecutor has accused Mr. Sussmann of lying during a September 2016 meeting with an F.B.I. official about Mr. Trump’s possible links to Russia.
The filing was ostensibly about potential conflicts of interest. But it also recounted a meeting at which Mr. Sussmann had presented other suspicions to the government. In February 2017, Mr. Sussmann told the C.I.A. about odd internet data suggesting that someone using a Russian-made smartphone may have been connecting to networks at Trump Tower and the White House, among other places.
Mr. Sussmann had obtained that information from a client, a technology executive named Rodney Joffe. Another paragraph in the court filing said that Mr. Joffe’s company, Neustar, had helped maintain internet-related servers for the White House, and that he and his associates “exploited this arrangement” by mining certain records to gather derogatory information about Mr. Trump.
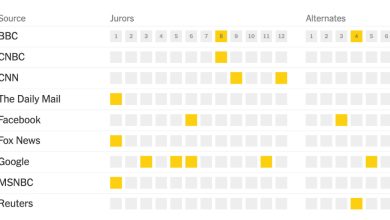
Citing this filing, Fox News inaccurately declared that Mr. Durham had said he had evidence that Hillary Clinton’s campaign had paid a technology company to “infiltrate” a White House server. The Washington Examiner claimed that this all meant there had been spying on Mr. Trump’s White House office. And when mainstream publications held back, Mr. Trump and his allies began shaming the news media.
“The press refuses to even mention the major crime that took place,” Mr. Trump said in a statement on Monday. “This in itself is a scandal, the fact that a story so big, so powerful and so important for the future of our nation is getting zero coverage from LameStream, is being talked about all over the world.”
There were many problems with all this. For one, much of this was not new: The New York Times had reported in October what Mr. Sussmann had told the C.I.A. about data suggesting that Russian-made smartphones, called YotaPhones, had been connecting to networks at Trump Tower and the White House, among other places.
The conservative media also skewed what the filing said. For example, Mr. Durham’s filing never used the word “infiltrate.” And it never claimed that Mr. Joffe’s company was being paid by the Clinton campaign.
Most important, contrary to the reporting, the filing never said the White House data that came under scrutiny was from the Trump era. According to lawyers for David Dagon, a Georgia Institute of Technology data scientist who helped develop the Yota analysis, the data — so-called DNS logs, which are records of when computers or smartphones have prepared to communicate with servers over the internet — came from Barack Obama’s presidency.
“What Trump and some news outlets are saying is wrong,” said Jody Westby and Mark Rasch, both lawyers for Mr. Dagon. “The cybersecurity researchers were investigating malware in the White House, not spying on the Trump campaign, and to our knowledge all of the data they used was nonprivate DNS data from before Trump took office.”
In a statement, a spokesperson for Mr. Joffe said that “contrary to the allegations in this recent filing,” he was apolitical, did not work for any political party, and had lawful access under a contract to work with others to analyze DNS data — including from the White House — for the purpose of hunting for security breaches or threats.
After Russians hacked networks for the White House and Democrats in 2015 and 2016, it went on, the cybersecurity researchers were “deeply concerned” to find data suggesting Russian-made YotaPhones were in proximity to the Trump campaign and the White House, so “prepared a report of their findings, which was subsequently shared with the C.I.A.”
A spokesman for Mr. Durham declined to comment.
Mr. Durham was assigned by the attorney general at the time, William P. Barr, to scour the Russia investigation for wrongdoing in May 2019 as Mr. Trump escalated his claims that he was the victim of a “deep state” conspiracy. But after nearly three years, he has not developed any cases against high-level government officials.
Instead, Mr. Durham has developed two cases against people associated with outside efforts to understand Russia’s election interference that put forward unproven, and sometimes thin or subsequently disproved, suspicions about purported links to Mr. Trump or his campaign.
Both cases are narrow — accusations of making false statements. One of those cases is against Mr. Sussmann, whom Mr. Durham has accused of lying during a September 2016 meeting with an F.B.I. official about Mr. Trump’s possible links to Russia.
(Mr. Durham says Mr. Sussmann falsely said he had no clients, but was there on behalf of both the Clinton campaign and Mr. Joffe. Mr. Sussman denies ever saying that, while maintaining he was only there on behalf of Mr. Joffe — not the campaign.)
Both Mr. Sussmann’s September 2016 meeting with the F.B.I. and the February 2017 meeting with the C.I.A. centered upon suspicions developed by cybersecurity researchers who specialize in sifting DNS data in search of hacking, botnets and other threats.
A military research organization had asked Georgia Tech researchers to help scrutinize a 2015 Russian malware attack on the White House’s network. After it emerged that Russia had hacked Democrats, they began hunting for signs of other Russian activity targeting people or organizations related to the election, using data provided by Neustar.
Mr. Sussmann’s meeting with the F.B.I. involved odd data the researchers said might indicate communications between the Trump Organization and Alfa Bank, a Kremlin-linked institution. The F.B.I. dismissed suspicions of a secret communications channel as unfounded. In the indictment of Mr. Sussmann, Mr. Durham insinuated that the researchers did not believe what they were saying. But lawyers for the researchers said that was false and that their clients believed their analysis.
The meeting with the C.I.A. involved odd data the researchers said indicated there had been communications with Yota servers in Russia coming from networks serving the White House; Trump Tower; Mr. Trump’s Central Park West apartment building; and Spectrum Health, a Michigan hospital company that also played a role in the Alfa Bank matter. The researchers also collaborated on that issue, according to Ms. Westby and Mr. Rasch, and Mr. Dagon had prepared a “white paper” explaining the analysis, which Mr. Sussmann later took to the C.I.A.
Mr. Durham’s filing also cast doubt on the researchers’ suggestion that interactions between devices in the United States and Yota servers were inherently suspicious, saying that there were more than three million such DNS logs from 2014 to 2017 — and that such logs from the White House dated back at least that long.
But Ms. Westby and Mr. Rasch reiterated that YotaPhones are extremely rare in the United States and portrayed three million DNS logs over three years as “paltry and small relative to the billions and billions” of logs associated with common devices like iPhones.
“Yota lookups are extremely concerning if they emanate from sensitive networks that require protection, such as government networks or people running for federal office,” they said.